让CentOS服务器支持https(安全http协议)
时间:2014-02-22 02:40 来源:51cto.com 作者:IT网
我们通常用“http://”这样的方式来访问网站,而此时传输的内容是可能被别人截获的,因为其内容是通过明文传输,所以在传递一些隐私、以及密码相关的信息时,就显得非常的不安全。在一些比较正式的网站、以及一些银行相关的网站中,一些需要提交隐私或者重要级别比较高的密码时,都采用“https://”的方式,来将传输内容加密,从而保证用户安全和避免隐私的泄漏。
今天在这里,我就通过mod_ssl来使我们的服务器也支持https。(环境:centos 5.5)
1、安装mod_ssl
通过yum来在线安装mod_ssl
[root@300second ~]# yum -y install mod_ssl ← 在线安装mod_ssl
Loaded plugins: fastestmirror
Loading mirror speeds from cached hostfile
* base: data.nicehosting.co.kr
* extras: data.nicehosting.co.kr
* updates: data.nicehosting.co.kr
addons | 951 B 00:00
addons/primary | 202 B 00:00
http://data.nicehosting.co.kr/os/CentOS/5.7/os/i386/repodata/repomd.xml: [Errno 14] HTTP Error 403: Forbidden
Trying other mirror.
base | 1.1 kB 00:00
base/primary | 961 kB 00:40
base 2705/2705
http://data.nicehosting.co.kr/os/CentOS/5.7/extras/i386/repodata/repomd.xml: [Errno 14] HTTP Error 403: Forbidden
Trying other mirror.
extras | 2.1 kB 00:00
extras/primary_db | 156 kB 00:06
http://data.nicehosting.co.kr/os/CentOS/5.7/updates/i386/repodata/repomd.xml: [Errno 14] HTTP Error 403: Forbidden
Trying other mirror.
updates | 1.9 kB 00:00
updates/primary_db | 290 kB 00:12
Setting up Install Process
Resolving Dependencies
--> Running transaction check
---> Package mod_ssl.i386 1:2.2.3-53.el5.centos.3 set to be updated
--> Processing Dependency: httpd = 2.2.3-53.el5.centos.3 for package: mod_ssl
--> Processing Dependency: libdistcache.so.1 for package: mod_ssl
--> Processing Dependency: libnal.so.1 for package: mod_ssl
--> Running transaction check
---> Package distcache.i386 0:1.4.5-14.1 set to be updated
---> Package httpd.i386 0:2.2.3-53.el5.centos.3 set to be updated
--> Finished Dependency Resolution
Dependencies Resolved
================================================================================
Package Arch Version Repository Size
================================================================================
Installing:
mod_ssl i386 1:2.2.3-53.el5.centos.3 updates 93 k
Installing for dependencies:
distcache i386 1.4.5-14.1 base 119 k
Updating for dependencies:
httpd i386 2.2.3-53.el5.centos.3 updates 1.2 M
Transaction Summary
================================================================================
Install 2 Package(s)
Upgrade 1 Package(s)
Total download size: 1.4 M
Downloading Packages:
(1/3): mod_ssl-2.2.3-53.el5.centos.3.i386.rpm | 93 kB 00:03
(2/3): distcache-1.4.5-14.1.i386.rpm | 119 kB 00:05
(3/3): httpd-2.2.3-53.el5.centos.3.i386.rpm | 1.2 MB 00:53
--------------------------------------------------------------------------------
Total 23 kB/s | 1.4 MB 01:02
warning: rpmts_HdrFromFdno: Header V3 DSA signature: NOKEY, key ID e8562897
updates/gpgkey | 1.5 kB 00:00
Importing GPG key 0xE8562897 "CentOS-5 Key (CentOS 5 Official Signing Key) <centos-5-key@centos.org>" from /etc/pki/rpm-gpg/RPM-GPG-KEY-CentOS-5
Running rpm_check_debug
Running Transaction Test
Finished Transaction Test
Transaction Test Succeeded
Running Transaction
Installing : distcache 1/4
Updating : httpd 2/4
Installing : mod_ssl 3/4
Cleanup : httpd 4/4
Installed:
mod_ssl.i386 1:2.2.3-53.el5.centos.3
Dependency Installed:
distcache.i386 0:1.4.5-14.1
Dependency Updated:
httpd.i386 0:2.2.3-53.el5.centos.3
Complete!
2、HTTP 服务器上配置mod_ssl
[1] 建立服务器密钥
[root@300second ~]# cd /etc/pki/tls/certs/ ← 进入HTTP服务器配置文件所在目录
[root@300second certs]# make server.key ← 建立服务器密钥
umask 77 ; \
/usr/bin/openssl genrsa -des3 1024 > server.key
Generating RSA private key, 1024 bit long modulus
................++++++
......++++++
e is 65537 (0x10001)
Enter pass phrase: ← 在这里输入口令
Verifying - Enter pass phrase: ← 确认口令,再次输入
[root@300second certs]# openssl rsa -in server.key -out server.key ← 从密钥中删除密码(以避免系统启动后被询问口令)
Enter pass phrase for server.key: ← 输入口令
writing RSA key
[2] 建立服务器公钥
[root@300second certs]# make server.csr ← 建立服务器密钥
umask 77 ; \
/usr/bin/openssl req -utf8 -new -key server.key -out server.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [GB]:CN ← 输入国名
State or Province Name (full name) [Berkshire]:Fujian ← 输入省名
Locality Name (eg, city) [Newbury]:Quanzhou ← 输入城市名
Organization Name (eg, company) [My Company Ltd]:www.51cto.com ← 输入组织名(任意)
Organizational Unit Name (eg, section) []: ← 不输入,直接回车
Common Name (eg, your name or your server's hostname) []:www.51cto.com ← 输入通称(任意)
Email Address []:300second@163.com ← 输入电子邮箱地址
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []: ← 不输入,直接回车
An optional company name []: ← 不输入,直接回车
[3] 建立服务器证书
[root@300second certs]# openssl x509 -in server.csr -out server.pem -req -signkey server.key -days 365 ← 建立服务器证书
Signature ok
subject=/C=CN/ST=Fujian/L=Quanzhou/O=www.51cto.com/CN=www.51cto.com/emailAddress=300second@163.com
Getting Private key
[root@300second certs]# chmod 400 server.* ← 修改权限为400
[4] 设置SSL
[root@300second certs]# vi /etc/httpd/conf.d/ssl.conf ← 修改SSL的设置文件
#DocumentRoot "/var/www/html" ← 找到这一行,将行首的“#”去掉
↓
DocumentRoot "/var/www/html" ← 变为此状态
[5] 重新启动HTTP服务,让SSL生效
[root@300second certs]# /etc/rc.d/init.d/httpd restart ← 重新启动HTTP服务器
停止 httpd: [ 确定 ]
启动 httpd: [ 确定]
3、测试SSL
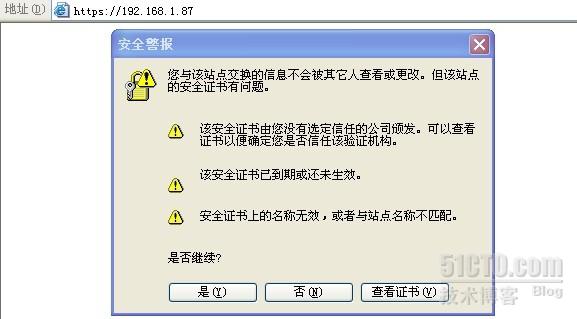
打开浏览器,在地址栏输入“https://服务器IP地址”或者“https://你的域名”后,如果出现提示安装服务器安全证书的窗口(如下所示),说明服务器已经支持SSL。
(责任编辑:IT)
我们通常用“http://”这样的方式来访问网站,而此时传输的内容是可能被别人截获的,因为其内容是通过明文传输,所以在传递一些隐私、以及密码相关的信息时,就显得非常的不安全。在一些比较正式的网站、以及一些银行相关的网站中,一些需要提交隐私或者重要级别比较高的密码时,都采用“https://”的方式,来将传输内容加密,从而保证用户安全和避免隐私的泄漏。 Dependencies Resolved
================================================================================
Transaction Summary
Total download size: 1.4 M
Installed:
Dependency Installed:
Dependency Updated:
Complete! |