centos 7 DenyHosts 安装 防暴力破解ssh登陆
时间:2016-06-08 14:03 来源:cnblogs.com 作者:xxx91hx
为了减少软件扫描ssh登陆 还是用这个比较好点 默认端口号22 也要改 登陆密码也不要使用 弱口令 123456 这样的
Description
DenyHosts is a python program that automatically blocks ssh attacks by adding entries to /etc/hosts.deny.
DenyHosts will also inform Linux administrators about offending hosts, attacked users and suspicious logins.
官网地址 http://denyhosts.sourceforge.net/
下载地址
http://sourceforge.net/projects/denyhosts/
http://jaist.dl.sourceforge.net/project/denyhosts/denyhosts/2.6/DenyHosts-2.6.tar.gz
[root@localhost src]# cd /usr/local/src
没有安装wget的请使用 yum -install -y wget 安装
下载DenyHosts
[root@localhost src]# wget http://jaist.dl.sourceforge.net/project/denyhosts/denyhosts/2.6/DenyHosts-2.6.tar.gz
--2015-03-28 15:39:28-- http://jaist.dl.sourceforge.net/project/denyhosts/denyhosts/2.6/DenyHosts-2.6.tar.gz
正在解析主机 jaist.dl.sourceforge.net (jaist.dl.sourceforge.net)... 150.65.7.130, 2001:df0:2ed:feed::feed
正在连接 jaist.dl.sourceforge.net (jaist.dl.sourceforge.net)|150.65.7.130|:80... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:42667 (42K) [application/x-gzip]
正在保存至: “DenyHosts-2.6.tar.gz”
100%[======================================>] 42,667 42.4KB/s 用时 1.0s
2015-03-28 15:39:30 (42.4 KB/s) - 已保存 “DenyHosts-2.6.tar.gz” [42667/42667])
解压DenyHosts
[root@localhost src]# tar -zxvf DenyHosts-2.6.tar.gz -C /usr/local/bin
DenyHosts-2.6/
DenyHosts-2.6/PKG-INFO
DenyHosts-2.6/denyhosts.py
DenyHosts-2.6/denyhosts.cfg-dist
DenyHosts-2.6/setup.py
DenyHosts-2.6/DenyHosts/
DenyHosts-2.6/DenyHosts/prefs.py
DenyHosts-2.6/DenyHosts/report.py
DenyHosts-2.6/DenyHosts/lockfile.py
DenyHosts-2.6/DenyHosts/__init__.py
DenyHosts-2.6/DenyHosts/plugin.py
DenyHosts-2.6/DenyHosts/denyfileutil.py
DenyHosts-2.6/DenyHosts/deny_hosts.py
DenyHosts-2.6/DenyHosts/regex.py
DenyHosts-2.6/DenyHosts/sync.py
DenyHosts-2.6/DenyHosts/counter.py
DenyHosts-2.6/DenyHosts/old-daemon.py
DenyHosts-2.6/DenyHosts/util.py
DenyHosts-2.6/DenyHosts/daemon.py
DenyHosts-2.6/DenyHosts/python_version.py
DenyHosts-2.6/DenyHosts/allowedhosts.py
DenyHosts-2.6/DenyHosts/filetracker.py
DenyHosts-2.6/DenyHosts/loginattempt.py
DenyHosts-2.6/DenyHosts/restricted.py
DenyHosts-2.6/DenyHosts/purgecounter.py
DenyHosts-2.6/DenyHosts/version.py
DenyHosts-2.6/DenyHosts/constants.py
DenyHosts-2.6/CHANGELOG.txt
DenyHosts-2.6/LICENSE.txt
DenyHosts-2.6/daemon-control-dist
DenyHosts-2.6/plugins/
DenyHosts-2.6/plugins/README.contrib
DenyHosts-2.6/plugins/shorewall_allow.sh
DenyHosts-2.6/plugins/shorewall_deny.sh
DenyHosts-2.6/plugins/test_deny.py
DenyHosts-2.6/scripts/
DenyHosts-2.6/scripts/restricted_from_invalid.py
DenyHosts-2.6/scripts/restricted_from_passwd.py
DenyHosts-2.6/README.txt
DenyHosts-2.6/MANIFEST.in
[root@localhost src]# cd /usr/local/bin
进入解压文件夹
cd DenyHosts-2.6

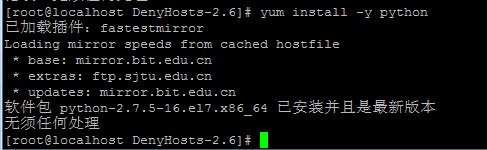
确认python编译工具安装
yun install -y python centos 7默认已经安装python-2.7.5
开始编译安装setup.py
python setup.py install
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
[root@localhost DenyHosts-2.6]# <strong>python setup.py install</strong>
running install
running build
running build_py
creating build
creating build/lib
creating build/lib/DenyHosts
copying DenyHosts/prefs.py -> build/lib/DenyHosts
copying DenyHosts/report.py -> build/lib/DenyHosts
copying DenyHosts/lockfile.py -> build/lib/DenyHosts
copying DenyHosts/__init__.py -> build/lib/DenyHosts
copying DenyHosts/plugin.py -> build/lib/DenyHosts
copying DenyHosts/denyfileutil.py -> build/lib/DenyHosts
copying DenyHosts/deny_hosts.py -> build/lib/DenyHosts
copying DenyHosts/regex.py -> build/lib/DenyHosts
copying DenyHosts/sync.py -> build/lib/DenyHosts
copying DenyHosts/counter.py -> build/lib/DenyHosts
copying DenyHosts/old-daemon.py -> build/lib/DenyHosts
copying DenyHosts/util.py -> build/lib/DenyHosts
copying DenyHosts/daemon.py -> build/lib/DenyHosts
copying DenyHosts/python_version.py -> build/lib/DenyHosts
copying DenyHosts/allowedhosts.py -> build/lib/DenyHosts
copying DenyHosts/filetracker.py -> build/lib/DenyHosts
copying DenyHosts/loginattempt.py -> build/lib/DenyHosts
copying DenyHosts/restricted.py -> build/lib/DenyHosts
copying DenyHosts/purgecounter.py -> build/lib/DenyHosts
copying DenyHosts/version.py -> build/lib/DenyHosts
copying DenyHosts/constants.py -> build/lib/DenyHosts
running build_scripts
creating build/scripts-2.7
copying and adjusting denyhosts.py -> build/scripts-2.7
changing mode of build/scripts-2.7/denyhosts.py from 644 to 755
running install_lib
creating /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/prefs.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/report.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/lockfile.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/__init__.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/plugin.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/denyfileutil.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/deny_hosts.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/regex.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/sync.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/counter.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/old-daemon.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/util.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/daemon.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/python_version.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/allowedhosts.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/filetracker.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/loginattempt.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/restricted.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/purgecounter.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/version.py -> /usr/lib/python2.7/site-packages/DenyHosts
copying build/lib/DenyHosts/constants.py -> /usr/lib/python2.7/site-packages/DenyHosts
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/prefs.py to prefs.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/report.py to report.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/lockfile.py to lockfile.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/__init__.py to __init__.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/plugin.py to plugin.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/denyfileutil.py to denyfileutil.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/deny_hosts.py to deny_hosts.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/regex.py to regex.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/sync.py to sync.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/counter.py to counter.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/old-daemon.py to old-daemon.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/util.py to util.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/daemon.py to daemon.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/python_version.py to python_version.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/allowedhosts.py to allowedhosts.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/filetracker.py to filetracker.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/loginattempt.py to loginattempt.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/restricted.py to restricted.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/purgecounter.py to purgecounter.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/version.py to version.pyc
byte-compiling /usr/lib/python2.7/site-packages/DenyHosts/constants.py to constants.pyc
running install_scripts
copying build/scripts-2.7/denyhosts.py -> /usr/bin
changing mode of /usr/bin/denyhosts.py to 755
running install_data
creating /usr/share/denyhosts
copying denyhosts.cfg-dist -> /usr/share/denyhosts
copying setup.py -> /usr/share/denyhosts
copying daemon-control-dist -> /usr/share/denyhosts
copying CHANGELOG.txt -> /usr/share/denyhosts
copying README.txt -> /usr/share/denyhosts
creating /usr/share/denyhosts/scripts
copying scripts/restricted_from_invalid.py -> /usr/share/denyhosts/scripts
copying scripts/restricted_from_passwd.py -> /usr/share/denyhosts/scripts
creating /usr/share/denyhosts/plugins
copying plugins/README.contrib -> /usr/share/denyhosts/plugins
copying plugins/shorewall_allow.sh -> /usr/share/denyhosts/plugins
copying plugins/shorewall_deny.sh -> /usr/share/denyhosts/plugins
copying plugins/test_deny.py -> /usr/share/denyhosts/plugins
copying LICENSE.txt -> /usr/share/denyhosts
running install_egg_info
Writing /usr/lib/python2.7/site-packages/DenyHosts-2.6-py2.7.egg-info
[root@localhost DenyHosts-2.6]#
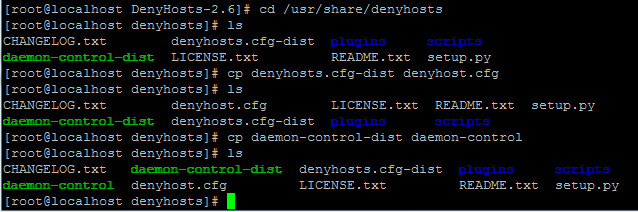
编辑配置文件denyhosts.cfg
[root@localhost DenyHosts-2.6]# cd /usr/share/denyhosts/
[root@localhost denyhosts]# cp denyhosts.cfg-dist denyhosts.cfg
[root@localhost denyhosts]# cp daemon-control-dist daemon-control
vi denyhost.cfg
该配置文件结构比较简单,简要说明主要参数如下:
PURGE_DENY:当一个IP被阻止以后,过多长时间被自动解禁。可选如3m(三分钟)、5h(5小时)、2d(两天)、8w(8周)、1y(一年);
PURGE_THRESHOLD:定义了某一IP最多被解封多少次。即某一IP由于暴力破解SSH密码被阻止/解封达到了PURGE_THRESHOLD次,则会被永久禁止;
BLOCK_SERVICE:需要阻止的服务名;
DENY_THRESHOLD_INVALID:某一无效用户名(不存在的用户)尝试多少次登录后被阻止;
DENY_THRESHOLD_VALID:某一有效用户名尝试多少次登陆后被阻止(比如账号正确但密码错误),root除外;
DENY_THRESHOLD_ROOT:root用户尝试登录多少次后被阻止;
HOSTNAME_LOOKUP:是否尝试解析源IP的域名;
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
393
394
395
396
397
398
399
400
401
402
403
404
405
406
407
408
409
410
411
412
413
414
415
416
417
418
419
420
421
422
423
424
425
426
427
428
429
430
431
432
433
434
435
436
437
438
439
440
441
442
443
444
445
446
447
448
449
450
451
452
453
454
455
456
457
458
459
460
461
462
463
464
465
466
467
468
469
470
471
472
473
474
475
476
477
478
479
480
481
482
483
484
485
486
487
488
489
490
491
492
493
494
495
496
497
498
499
500
501
502
503
504
505
506
507
508
509
510
511
512
513
514
515
516
517
518
519
520
521
522
523
524
525
526
527
528
529
530
531
532
533
534
535
536
537
538
539
540
541
542
543
544
545
546
547
548
549
550
551
552
553
554
555
556
557
558
559
560
561
562
563
564
565
566
567
568
569
570
571
572
573
574
575
576
577
578
579
580
581
582
583
584
585
586
587
588
589
590
591
592
593
594
595
596
597
598
599
600
601
602
603
604
605
606
607
608
609
610
611
612
613
614
615
616
617
618
[root@localhost denyhosts]# vi denyhost.cfg
############ THESE SETTINGS ARE REQUIRED ############
########################################################################
#
# SECURE_LOG: the log file that contains sshd logging info
# if you are not sure, grep "sshd:" /var/log/*
#
# The file to process can be overridden with the --file command line
# argument
#
# Redhat or Fedora Core:
SECURE_LOG = /var/log/secure
#
# Mandrake, FreeBSD or OpenBSD:
#SECURE_LOG = /var/log/auth.log
#
# SuSE:
#SECURE_LOG = /var/log/messages
#
# Mac OS X (v10.4 or greater -
# also refer to: http://www.denyhosts.net/faq.html#macos
#SECURE_LOG = /private/var/log/asl.log
#
# Mac OS X (v10.3 or earlier):
#SECURE_LOG=/private/var/log/system.log
#
########################################################################
########################################################################
#
# HOSTS_DENY: the file which contains restricted host access information
#
# Most operating systems:
HOSTS_DENY = /etc/hosts.deny
#
# Some BSD (FreeBSD) Unixes:
#HOSTS_DENY = /etc/hosts.allow
#
# Another possibility (also see the next option):
#HOSTS_DENY = /etc/hosts.evil
#######################################################################
########################################################################
#
# PURGE_DENY: removed HOSTS_DENY entries that are older than this time
# when DenyHosts is invoked with the --purge flag
#
# format is: i[dhwmy]
# Where 'i' is an integer (eg. 7)
# 'm' = minutes
# 'h' = hours
# 'd' = days
# 'w' = weeks
# 'y' = years
#
# never purge:
PURGE_DENY = 100y
#
# purge entries older than 1 week
#PURGE_DENY = 1w
#
# purge entries older than 5 days
#PURGE_DENY = 5d
#######################################################################
#######################################################################
#
# PURGE_THRESHOLD: defines the maximum times a host will be purged.
# Once this value has been exceeded then this host will not be purged.
# Setting this parameter to 0 (the default) disables this feature.
#
# default: a denied host can be purged/re-added indefinitely
#PURGE_THRESHOLD = 0
#
# a denied host will be purged at most 2 times.
#PURGE_THRESHOLD = 2
#
#######################################################################
#######################################################################
#
# BLOCK_SERVICE: the service name that should be blocked in HOSTS_DENY
#
# man 5 hosts_access for details
#
# eg. sshd: 127.0.0.1 # will block sshd logins from 127.0.0.1
#
# To block all services for the offending host:
#BLOCK_SERVICE = ALL
# To block only sshd:
BLOCK_SERVICE = sshd
# To only record the offending host and nothing else (if using
# an auxilary file to list the hosts). Refer to:
# http://denyhosts.sourceforge.net/faq.html#aux
#BLOCK_SERVICE =
#
#######################################################################
#######################################################################
#
# DENY_THRESHOLD_INVALID: block each host after the number of failed login
# attempts has exceeded this value. This value applies to invalid
# user login attempts (eg. non-existent user accounts)
#
DENY_THRESHOLD_INVALID = 5
#
#######################################################################
#######################################################################
#
# DENY_THRESHOLD_VALID: block each host after the number of failed
# login attempts has exceeded this value. This value applies to valid
# user login attempts (eg. user accounts that exist in /etc/passwd) except
# for the "root" user
#
DENY_THRESHOLD_VALID = 10
#
#######################################################################
#######################################################################
#
# DENY_THRESHOLD_ROOT: block each host after the number of failed
# login attempts has exceeded this value. This value applies to
# "root" user login attempts only.
#
DENY_THRESHOLD_ROOT = 10
#
#######################################################################
#######################################################################
#
# DENY_THRESHOLD_RESTRICTED: block each host after the number of failed
# login attempts has exceeded this value. This value applies to
# usernames that appear in the WORK_DIR/restricted-usernames file only.
#
DENY_THRESHOLD_RESTRICTED = 1
#
#######################################################################
#######################################################################
#
# WORK_DIR: the path that DenyHosts will use for writing data to
# (it will be created if it does not already exist).
#
# Note: it is recommended that you use an absolute pathname
# for this value (eg. /home/foo/denyhosts/data)
#
WORK_DIR = /usr/share/denyhosts/data
#
#######################################################################
#######################################################################
#
# SUSPICIOUS_LOGIN_REPORT_ALLOWED_HOSTS
#
# SUSPICIOUS_LOGIN_REPORT_ALLOWED_HOSTS=YES|NO
# If set to YES, if a suspicious login attempt results from an allowed-host
# then it is considered suspicious. If this is NO, then suspicious logins
# from allowed-hosts will not be reported. All suspicious logins from
# ip addresses that are not in allowed-hosts will always be reported.
#
SUSPICIOUS_LOGIN_REPORT_ALLOWED_HOSTS=YES
######################################################################
######################################################################
#
# HOSTNAME_LOOKUP
#
# HOSTNAME_LOOKUP=YES|NO
# If set to YES, for each IP address that is reported by Denyhosts,
# the corresponding hostname will be looked up and reported as well
# (if available).
#
HOSTNAME_LOOKUP=YES
#
######################################################################
######################################################################
#
# LOCK_FILE
#
# LOCK_FILE=/path/denyhosts
# If this file exists when DenyHosts is run, then DenyHosts will exit
# immediately. Otherwise, this file will be created upon invocation
# and deleted upon exit. This ensures that only one instance is
# running at a time.
#
# Redhat/Fedora:
LOCK_FILE = /var/lock/subsys/denyhosts
#
# Debian
#LOCK_FILE = /var/run/denyhosts.pid
#
# Misc
#LOCK_FILE = /tmp/denyhosts.lock
#
######################################################################
############ THESE SETTINGS ARE OPTIONAL ############
#######################################################################
#
# ADMIN_EMAIL: if you would like to receive emails regarding newly
# restricted hosts and suspicious logins, set this address to
# match your email address. If you do not want to receive these reports
# leave this field blank (or run with the --noemail option)
#
# Multiple email addresses can be delimited by a comma, eg:
# ADMIN_EMAIL = foo@bar.com, bar@foo.com, etc@foobar.com
#
ADMIN_EMAIL =
#
#######################################################################
#######################################################################
#######################################################################
#
# SMTP_HOST and SMTP_PORT: if DenyHosts is configured to email
# reports (see ADMIN_EMAIL) then these settings specify the
# email server address (SMTP_HOST) and the server port (SMTP_PORT)
#
#
SMTP_HOST = localhost
SMTP_PORT = 25
#
#######################################################################
#######################################################################
#
# SMTP_USERNAME and SMTP_PASSWORD: set these parameters if your
# smtp email server requires authentication
#
#SMTP_USERNAME=foo
#SMTP_PASSWORD=bar
#
######################################################################
#######################################################################
#
# SMTP_FROM: you can specify the "From:" address in messages sent
# from DenyHosts when it reports thwarted abuse attempts
#
SMTP_FROM = DenyHosts <nobody@localhost>
#
#######################################################################
#######################################################################
#
# SMTP_SUBJECT: you can specify the "Subject:" of messages sent
# by DenyHosts when it reports thwarted abuse attempts
SMTP_SUBJECT = DenyHosts Report
#
######################################################################
######################################################################
#
# SMTP_DATE_FORMAT: specifies the format used for the "Date:" header
# when sending email messages.
#
# for possible values for this parameter refer to: man strftime
#
# the default:
#
#SMTP_DATE_FORMAT = %a, %d %b %Y %H:%M:%S %z
#
######################################################################
######################################################################
#
# SYSLOG_REPORT
#
# SYSLOG_REPORT=YES|NO
# If set to yes, when denied hosts are recorded the report data
# will be sent to syslog (syslog must be present on your system).
# The default is: NO
#
#SYSLOG_REPORT=NO
#
#SYSLOG_REPORT=YES
#
######################################################################
######################################################################
#
# ALLOWED_HOSTS_HOSTNAME_LOOKUP
#
# ALLOWED_HOSTS_HOSTNAME_LOOKUP=YES|NO
# If set to YES, for each entry in the WORK_DIR/allowed-hosts file,
# the hostname will be looked up. If your versions of tcp_wrappers
# and sshd sometimes log hostnames in addition to ip addresses
# then you may wish to specify this option.
#
#ALLOWED_HOSTS_HOSTNAME_LOOKUP=NO
#
######################################################################
######################################################################
#
# AGE_RESET_VALID: Specifies the period of time between failed login
# attempts that, when exceeded will result in the failed count for
# this host to be reset to 0. This value applies to login attempts
# to all valid users (those within /etc/passwd) with the
# exception of root. If not defined, this count will never
# be reset.
#
# See the comments in the PURGE_DENY section (above)
# for details on specifying this value or for complete details
# refer to: http://denyhosts.sourceforge.net/faq.html#timespec
#
AGE_RESET_VALID=5d
#
######################################################################
######################################################################
#
# AGE_RESET_ROOT: Specifies the period of time between failed login
# attempts that, when exceeded will result in the failed count for
# this host to be reset to 0. This value applies to all login
# attempts to the "root" user account. If not defined,
# this count will never be reset.
#
# See the comments in the PURGE_DENY section (above)
# for details on specifying this value or for complete details
# refer to: http://denyhosts.sourceforge.net/faq.html#timespec
#
AGE_RESET_ROOT=25d
#
######################################################################
######################################################################
#
# AGE_RESET_RESTRICTED: Specifies the period of time between failed login
# attempts that, when exceeded will result in the failed count for
# this host to be reset to 0. This value applies to all login
# attempts to entries found in the WORK_DIR/restricted-usernames file.
# If not defined, the count will never be reset.
#
# See the comments in the PURGE_DENY section (above)
# for details on specifying this value or for complete details
# refer to: http://denyhosts.sourceforge.net/faq.html#timespec
#
AGE_RESET_RESTRICTED=25d
#
######################################################################
######################################################################
#
# AGE_RESET_INVALID: Specifies the period of time between failed login
# attempts that, when exceeded will result in the failed count for
# this host to be reset to 0. This value applies to login attempts
# made to any invalid username (those that do not appear
# in /etc/passwd). If not defined, count will never be reset.
#
# See the comments in the PURGE_DENY section (above)
# for details on specifying this value or for complete details
# refer to: http://denyhosts.sourceforge.net/faq.html#timespec
#
AGE_RESET_INVALID=10d
#
######################################################################
######################################################################
#
# RESET_ON_SUCCESS: If this parameter is set to "yes" then the
# failed count for the respective ip address will be reset to 0
# if the login is successful.
#
# The default is RESET_ON_SUCCESS = no
#
#RESET_ON_SUCCESS = yes
#
#####################################################################
######################################################################
#
# PLUGIN_DENY: If set, this value should point to an executable
# program that will be invoked when a host is added to the
# HOSTS_DENY file. This executable will be passed the host
# that will be added as it's only argument.
#
#PLUGIN_DENY=/usr/bin/true
#
######################################################################
######################################################################
#
# PLUGIN_PURGE: If set, this value should point to an executable
# program that will be invoked when a host is removed from the
# HOSTS_DENY file. This executable will be passed the host
# that is to be purged as it's only argument.
#
#PLUGIN_PURGE=/usr/bin/true
#
######################################################################
######################################################################
#
# USERDEF_FAILED_ENTRY_REGEX: if set, this value should contain
# a regular expression that can be used to identify additional
# hackers for your particular ssh configuration. This functionality
# extends the built-in regular expressions that DenyHosts uses.
# This parameter can be specified multiple times.
# See this faq entry for more details:
# http://denyhosts.sf.net/faq.html#userdef_regex
#
#USERDEF_FAILED_ENTRY_REGEX=
#
#
######################################################################
######### THESE SETTINGS ARE SPECIFIC TO DAEMON MODE ##########
#######################################################################
#
# DAEMON_LOG: when DenyHosts is run in daemon mode (--daemon flag)
# this is the logfile that DenyHosts uses to report it's status.
# To disable logging, leave blank. (default is: /var/log/denyhosts)
#
DAEMON_LOG = /var/log/denyhosts
#
# disable logging:
#DAEMON_LOG =
#
######################################################################
#######################################################################
#
# DAEMON_LOG_TIME_FORMAT: when DenyHosts is run in daemon mode
# (--daemon flag) this specifies the timestamp format of
# the DAEMON_LOG messages (default is the ISO8061 format:
# ie. 2005-07-22 10:38:01,745)
#
# for possible values for this parameter refer to: man strftime
#
# Jan 1 13:05:59
#DAEMON_LOG_TIME_FORMAT = %b %d %H:%M:%S
#
# Jan 1 01:05:59
#DAEMON_LOG_TIME_FORMAT = %b %d %I:%M:%S
#
######################################################################
#######################################################################
#
# DAEMON_LOG_MESSAGE_FORMAT: when DenyHosts is run in daemon mode
# (--daemon flag) this specifies the message format of each logged
# entry. By default the following format is used:
#
# %(asctime)s - %(name)-12s: %(levelname)-8s %(message)s
#
# Where the "%(asctime)s" portion is expanded to the format
# defined by DAEMON_LOG_TIME_FORMAT
#
# This string is passed to python's logging.Formatter contstuctor.
# For details on the possible format types please refer to:
# http://docs.python.org/lib/node357.html
#
# This is the default:
#DAEMON_LOG_MESSAGE_FORMAT = %(asctime)s - %(name)-12s: %(levelname)-8s %(message)s
#
#
######################################################################
#######################################################################
#
# DAEMON_SLEEP: when DenyHosts is run in daemon mode (--daemon flag)
# this is the amount of time DenyHosts will sleep between polling
# the SECURE_LOG. See the comments in the PURGE_DENY section (above)
# for details on specifying this value or for complete details
# refer to: http://denyhosts.sourceforge.net/faq.html#timespec
#
#
DAEMON_SLEEP = 30s
#
#######################################################################
#######################################################################
#
# DAEMON_PURGE: How often should DenyHosts, when run in daemon mode,
# run the purge mechanism to expire old entries in HOSTS_DENY
# This has no effect if PURGE_DENY is blank.
#
DAEMON_PURGE = 1h
#
#######################################################################
######### THESE SETTINGS ARE SPECIFIC TO ##########
######### DAEMON SYNCHRONIZATION ##########
#######################################################################
#
# Synchronization mode allows the DenyHosts daemon the ability
# to periodically send and receive denied host data such that
# DenyHosts daemons worldwide can automatically inform one
# another regarding banned hosts. This mode is disabled by
# default, you must uncomment SYNC_SERVER to enable this mode.
#
# for more information, please refer to:
# http:/denyhosts.sourceforge.net/faq.html#sync
#
#######################################################################
#######################################################################
#
# SYNC_SERVER: The central server that communicates with DenyHost
# daemons. Currently, denyhosts.net is the only available server
# however, in the future, it may be possible for organizations to
# install their own server for internal network synchronization
#
# To disable synchronization (the default), do nothing.
#
# To enable synchronization, you must uncomment the following line:
#SYNC_SERVER = http://xmlrpc.denyhosts.net:9911
#
#######################################################################
#######################################################################
#
# SYNC_INTERVAL: the interval of time to perform synchronizations if
# SYNC_SERVER has been uncommented. The default is 1 hour.
#
#SYNC_INTERVAL = 1h
#
#######################################################################
#######################################################################
#
# SYNC_UPLOAD: allow your DenyHosts daemon to transmit hosts that have
# been denied? This option only applies if SYNC_SERVER has
# been uncommented.
# The default is SYNC_UPLOAD = yes
#
#SYNC_UPLOAD = no
#SYNC_UPLOAD = yes
#
#######################################################################
#######################################################################
#
# SYNC_DOWNLOAD: allow your DenyHosts daemon to receive hosts that have
# been denied by others? This option only applies if SYNC_SERVER has
# been uncommented.
# The default is SYNC_DOWNLOAD = yes
#
#SYNC_DOWNLOAD = no
#SYNC_DOWNLOAD = yes
#
#
#
#######################################################################
#######################################################################
#
# SYNC_DOWNLOAD_THRESHOLD: If SYNC_DOWNLOAD is enabled this parameter
# filters the returned hosts to those that have been blocked this many
# times by others. That is, if set to 1, then if a single DenyHosts
# server has denied an ip address then you will receive the denied host.
#
# See also SYNC_DOWNLOAD_RESILIENCY
#
#SYNC_DOWNLOAD_THRESHOLD = 10
#
# The default is SYNC_DOWNLOAD_THRESHOLD = 3
#
#SYNC_DOWNLOAD_THRESHOLD = 3
#
#######################################################################
#######################################################################
#
# SYNC_DOWNLOAD_RESILIENCY: If SYNC_DOWNLOAD is enabled then the
# value specified for this option limits the downloaded data
# to this resiliency period or greater.
#
# Resiliency is defined as the timespan between a hackers first known
# attack and it's most recent attack. Example:
#
# If the centralized denyhosts.net server records an attack at 2 PM
# and then again at 5 PM, specifying a SYNC_DOWNLOAD_RESILIENCY = 4h
# will not download this ip address.
#
# However, if the attacker is recorded again at 6:15 PM then the
# ip address will be downloaded by your DenyHosts instance.
#
# This value is used in conjunction with the SYNC_DOWNLOAD_THRESHOLD
# and only hosts that satisfy both values will be downloaded.
# This value has no effect if SYNC_DOWNLOAD_THRESHOLD = 1
#
# The default is SYNC_DOWNLOAD_RESILIENCY = 5h (5 hours)
#
# Only obtain hackers that have been at it for 2 days or more:
#SYNC_DOWNLOAD_RESILIENCY = 2d
# Only obtain hackers that have been at it for 5 hours or more:
#SYNC_DOWNLOAD_RESILIENCY = 5h
#
#######################################################################
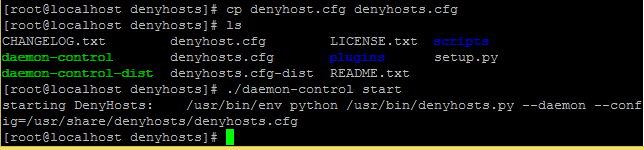
启动DenyHosts和添加自启动
目录 /usr/share/denyhosts
./daemon-control start
添加自启动服务
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
[root@localhost denyhosts]# cd /etc/init.d
[root@localhost init.d]# ls
functions iprdump iprinit iprupdate netconsole network README
[root@localhost init.d]# ln -s /usr/share/denyhosts/daemon-control denyhosts
[root@localhost init.d]# ls
denyhosts functions iprdump iprinit iprupdate netconsole network README
[root@localhost init.d]# chkconfig --add denyhosts
[root@localhost init.d]# chkconfig denyhosts on
[root@localhost init.d]# chkconfig --list denyhosts
注意:该输出结果只显示 SysV 服务,并不包含原生 systemd 服务。SysV 配置数据可能被原生 systemd 配置覆盖。
如果您想列出 systemd 服务,请执行 'systemctl list-unit-files'。
欲查看对特定 target 启用的服务请执行
'systemctl list-dependencies [target]'。
denyhosts 0:关 1:关 2:开 3:开 4:开 5:开 6:关
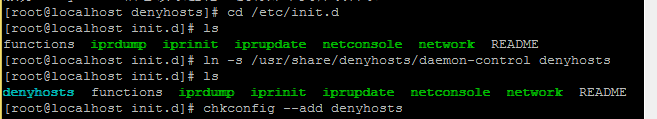
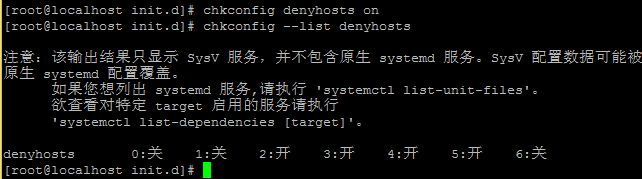
这样就完成了
(责任编辑:IT)
为了减少软件扫描ssh登陆 还是用这个比较好点 默认端口号22 也要改 登陆密码也不要使用 弱口令 123456 这样的 Description
DenyHosts is a python program that automatically blocks ssh attacks by adding entries to /etc/hosts.deny.
官网地址 http://denyhosts.sourceforge.net/ 下载地址 http://sourceforge.net/projects/denyhosts/
http://jaist.dl.sourceforge.net/project/denyhosts/denyhosts/2.6/DenyHosts-2.6.tar.gz
[root@localhost src]# cd /usr/local/src 没有安装wget的请使用 yum -install -y wget 安装 下载DenyHosts
[root@localhost src]# wget http://jaist.dl.sourceforge.net/project/denyhosts/denyhosts/2.6/DenyHosts-2.6.tar.gz 100%[======================================>] 42,667 42.4KB/s 用时 1.0s 2015-03-28 15:39:30 (42.4 KB/s) - 已保存 “DenyHosts-2.6.tar.gz” [42667/42667])
解压DenyHosts
[root@localhost src]# tar -zxvf DenyHosts-2.6.tar.gz -C /usr/local/bin
进入解压文件夹 cd DenyHosts-2.6
确认python编译工具安装 yun install -y python centos 7默认已经安装python-2.7.5
开始编译安装setup.py python setup.py install
编辑配置文件denyhosts.cfg [root@localhost DenyHosts-2.6]# cd /usr/share/denyhosts/ [root@localhost denyhosts]# cp denyhosts.cfg-dist denyhosts.cfg [root@localhost denyhosts]# cp daemon-control-dist daemon-control
vi denyhost.cfg 该配置文件结构比较简单,简要说明主要参数如下: PURGE_DENY:当一个IP被阻止以后,过多长时间被自动解禁。可选如3m(三分钟)、5h(5小时)、2d(两天)、8w(8周)、1y(一年); PURGE_THRESHOLD:定义了某一IP最多被解封多少次。即某一IP由于暴力破解SSH密码被阻止/解封达到了PURGE_THRESHOLD次,则会被永久禁止; BLOCK_SERVICE:需要阻止的服务名; DENY_THRESHOLD_INVALID:某一无效用户名(不存在的用户)尝试多少次登录后被阻止; DENY_THRESHOLD_VALID:某一有效用户名尝试多少次登陆后被阻止(比如账号正确但密码错误),root除外; DENY_THRESHOLD_ROOT:root用户尝试登录多少次后被阻止; HOSTNAME_LOOKUP:是否尝试解析源IP的域名;
启动DenyHosts和添加自启动 目录 /usr/share/denyhosts ./daemon-control start
添加自启动服务
这样就完成了 (责任编辑:IT) |